Continuing to previous post, download the Damn Insecure and Vulnerable App (DIVA). Download the tar file from the below location and unzip for .apk file:
http://www.payatu.com/storage/2016/01/diva-beta.tar.gz
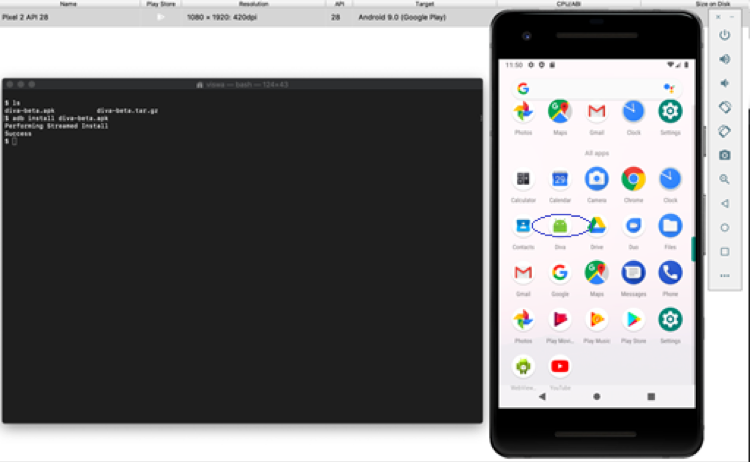
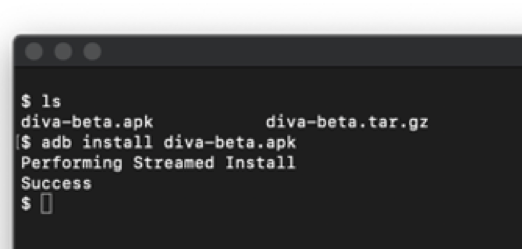
Installing .apk into Emulator
adb install diva-beta.apk – New App Diva installed in Android device
If installation has completed successfully, following screen should be displayed when starting the App “Diva”. Click on 1. Insecure Logging exercise:
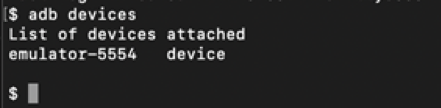
Screen navigates to Insecure Logging page, where user is expected to enter credit card number and click on Checkout. As this vulnerability is about logs, check the emulator is connected to adb:
| adb devices
|
Now the log can be seen using the command, enter card number in emulator “123456” and click on Checkout. The log should be recording the value “123456” which is a credit card number.
| adb logcat
|
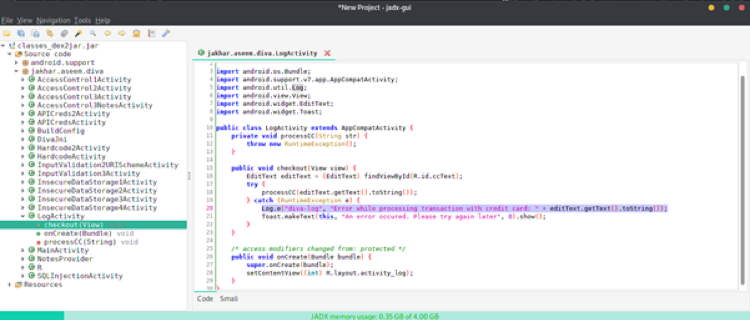
Walk through the source code after decompiling the App. Process to decompile:
- Rename .apk file as .zip and unzip the file.
- Using dex2jar tool, convert the extracted “classes.dex” to “.jar” file.
- Open the .jar file using Jadx tool for viewing the source code.
Find and navigate to LogActivity.class, checkout method processes an exception in case of issue, and error message is logged into log file. Normally during development stage of the lifecycle, developers would add messages to log file for debugging purposes. There are scenarios where the app is deployed into production without removing log messages.
Remediation
The developer should remove the Log class during final build. By adding the following line to ProGuard config, it will help in preventing log information. ProGuard helps to obfuscate and optimise your code into release version.
| -assumenosideeffects class android.util.Log{*;} |
An alternative way to remediate is to use Log.d inside a wrapper class by implementing BuildConfig.Debug variable as build type to differentiate if the build is Release or Debug build:
| public class LogUtils {
public static void LOGD (final String tag, String message) { if (BuildConfig.DEBUG) { Log.d(tag, message); } } } LogUtils.LOGD(TAG, “MyActivity.onCreate debug message”); |
|---|
In the next article we’ll look at different kinds of vulnerabilities in Mobile applications.